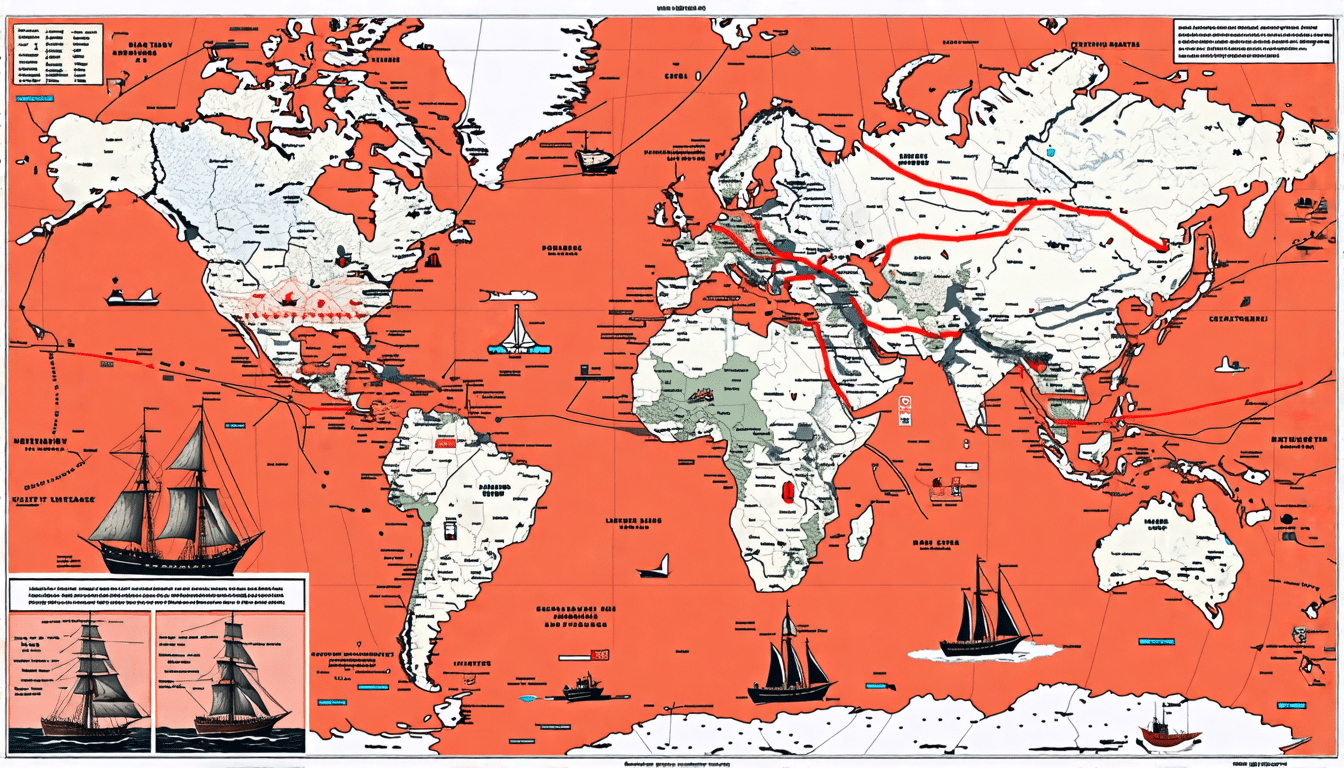
In the vast expanse of our planet’s oceans, strategic maritime zones play a crucial role in the seamless operation of global trade and the maintenance of international security. These significant regions serve as arteries of global commerce, with ships navigating through them to transport essential goods and commodities between continents. However, alongside their importance comes inherent vulnerability, as these vital waterways often attract unlawful activities, notably piracy. Understanding strategic maritime zones and their pivotal impact on global dynamics is essential for comprehending the intricate web of geopolitical relations that they influence. This article delves into the heart of these zones, shedding light on the piracy-prone areas that pose formidable challenges to maritime security, and examining the historical and modern-day efforts to counteract the menace of piracy. By identifying and analyzing key hotspots like the Gulf of Aden, the Strait of Malacca, and the West African coast, we aim to provide a comprehensive insight into the ongoing battle against piracy, drawing attention to the strategies implemented to safeguard these crucial maritime passages.
Understanding Strategic Maritime Zones
Defining Strategic Maritime Zones
Strategic maritime zones are defined as critical areas of oceans and seas that hold significant importance for global navigation, trade, and security. These zones often encompass crucial shipping routes, chokepoints, and regions with abundant marine resources. Their strategic nature makes them pivotal in the movement of goods, energy supplies, and military assets, thereby playing a fundamental role in the global economy.
One prime example of a strategic maritime zone is the Strait of Hormuz. This narrow passage between the Persian Gulf and the Gulf of Oman is one of the most vital oil transit chokepoints in the world. Similarly, the Panama Canal, connecting the Atlantic and Pacific Oceans, serves as an indispensable artery for international maritime trade.
Importance for Global Trade and Security
The importance of strategic maritime zones for global trade cannot be overstated. Approximately 90% of the world’s goods are transported by sea, making the smooth operation of these zones essential. Key commodities such as oil, natural gas, coal, and agricultural products traverse these routes, impacting economies worldwide. Disruptions in these areas can lead to significant economic and energy crises.
One illustrative case is the Suez Canal, an artificial waterway in Egypt that links the Mediterranean Sea to the Red Sea. As one of the most heavily used waterways in the world, the Suez Canal records thousands of transits annually. An illustration of its critical status was highlighted during the 2021 blockage by the Ever Given container ship, which underscored the global ramifications of interruptions in strategic maritime routes.
Security in strategic maritime zones is equally paramount. These regions are often the focus of naval operations and international maritime security efforts. Governments deploy substantial naval resources to safeguard these zones, ensuring safe passage for commercial vessels and preventing threats such as piracy, smuggling, and territorial disputes.
Influence on Geopolitical Relations
The strategic significance of maritime zones carries considerable weight in geopolitics. Control over these areas can enhance a nation’s influence and power, often leading to tensions and conflicts. Consequently, maritime zones have historically been at the center of territorial disputes and international negotiations.
For instance, the South China Sea is a strategic maritime zone characterized by overlapping territorial claims from China, Vietnam, the Philippines, Malaysia, Taiwan, and Brunei. This body of water not only is rich in fish stocks and potential energy reserves but also is a strategic navigation route where a significant portion of the world’s shipping passes through. The geopolitical disputes in this area underscore the delicate balance between national interests and international law.
Moreover, alliances and partnerships are frequently forged with strategic maritime zones in mind. Nations with well-established maritime capabilities often extend their influence through naval bases and bilateral maritime agreements. For example, the United States has established military bases in key locations such as the naval base in Bahrain, ensuring a continuous strategic presence in the Persian Gulf.
In summary, understanding strategic maritime zones is essential for appreciating their role in global trade, security, and geopolitical relations. These zones are the lifelines of maritime commerce, potential flashpoints for conflict, and key elements in the strategic calculations of nations around the world. Their influence extends beyond economic considerations, affecting military strategies, diplomatic relations, and international collaboration.
https://www.virtualmaritime.academy/vma-courses/
Identifying and Analyzing Piracy-Prone Areas
Understanding piracy-prone areas is crucial for enhancing maritime security and mitigating threats to global trade. Historically, piracy has been concentrated in specific regions, often influenced by geographic, economic, and political factors.
Historical Overview of Global Piracy Hotspots
Throughout history, several maritime zones have gained notoriety as piracy hotspots. These regions were typically characterized by important trade routes, political instability, and limited law enforcement capabilities.
The Caribbean Sea during the 17th and 18th centuries was infamous for pirate activities. Buccaneers and privateers who were originally sanctioned by European powers turned rogue, preying on merchant ships transporting valuable goods such as gold and silver.
In the 19th century, piracy emerged in the South China Sea due to the vast archipelagic geography, lack of strong naval presence, and the lucrative trade routes between Asia and the Americas. This region remains a concern today, with modern-day pirates targeting ships for ransom and theft.
Another historical hotspot was the Barbary Coast in North Africa. Pirates known as Barbary Corsairs threatened Mediterranean shipping routes, capturing vessels and enslaving sailors. Naval campaigns and treaties in the early 19th century eventually quelled this piracy wave.
Case Studies: Notable Piracy-Prone Maritime Zones
Gulf of Aden
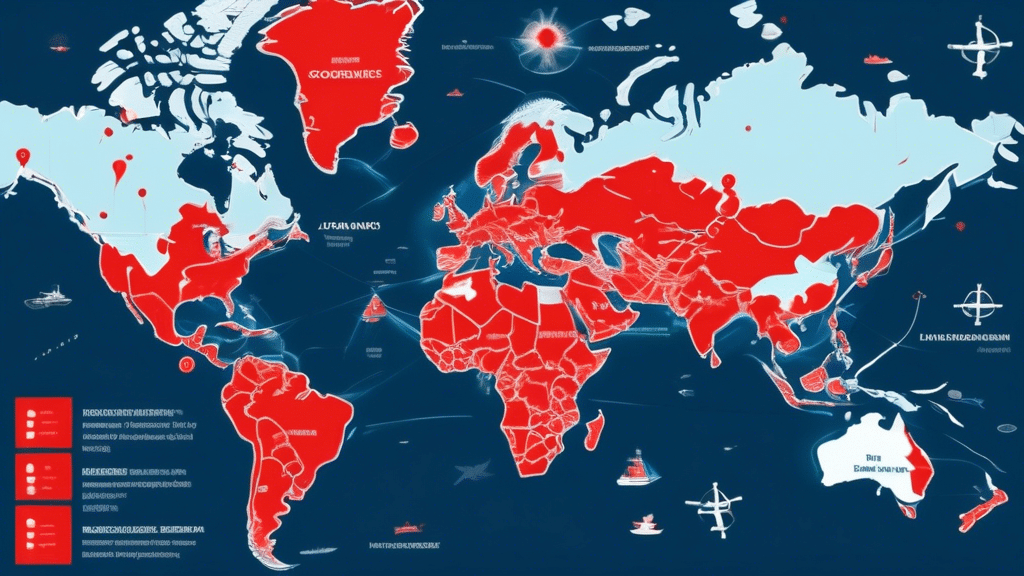
The Gulf of Aden, located between Yemen and Somalia, has been a focal point for maritime piracy, particularly in the 21st century. The strategic importance of the Gulf, connecting the Indian Ocean to the Red Sea and the Suez Canal, makes it a vital artery for international shipping. Pirates based in Somalia exploited the country’s political instability and lack of effective governance, launching attacks on commercial vessels, often demanding hefty ransoms. The international community responded with increased naval patrols and coordination through initiatives like the Combined Maritime Forces (CMF) and EU NAVFOR’s Operation Atalanta.
Strait of Malacca
The Strait of Malacca, situated between the Malay Peninsula and the Indonesian island of Sumatra, is one of the busiest and most strategic waterways in the world, accounting for more than one-fourth of global maritime trade. Its narrow strait makes vessels vulnerable to piracy. Historically, pirates took advantage of the high traffic and limited safe passageways to hijack ships and steal cargo. Despite significant improvements in regional cooperation and enhanced naval presence, piracy remains a threat in this area. Recent efforts by Malaysia, Indonesia, and Singapore, including the Malacca Strait Patrol (MSP) Joint Coordinating Committee, have helped to reduce incidents through coordinated patrols and information sharing.
West African Coast
The Gulf of Guinea, located along the West African coast, has seen a dramatic increase in pirate activity in recent years. The region’s rich oil deposits and the widespread illicit trade have attracted criminal networks. Pirates in this area are often well-organized, conducting hijacking, kidnapping for ransom, and cargo theft. The lack of effective maritime security infrastructure and regional cooperation exacerbates the problem. Organizations such as the Gulf of Guinea Maritime Institute and international naval forces are working to improve security through capacity building, joint exercises, and better coordination among affected countries.
Modern Challenges and Countermeasures in Piracy Prevention
In contemporary times, piracy presents several new challenges. The evolution of pirate tactics, political instability, and economic disparity contribute to the persistence and adaptation of piracy activities.
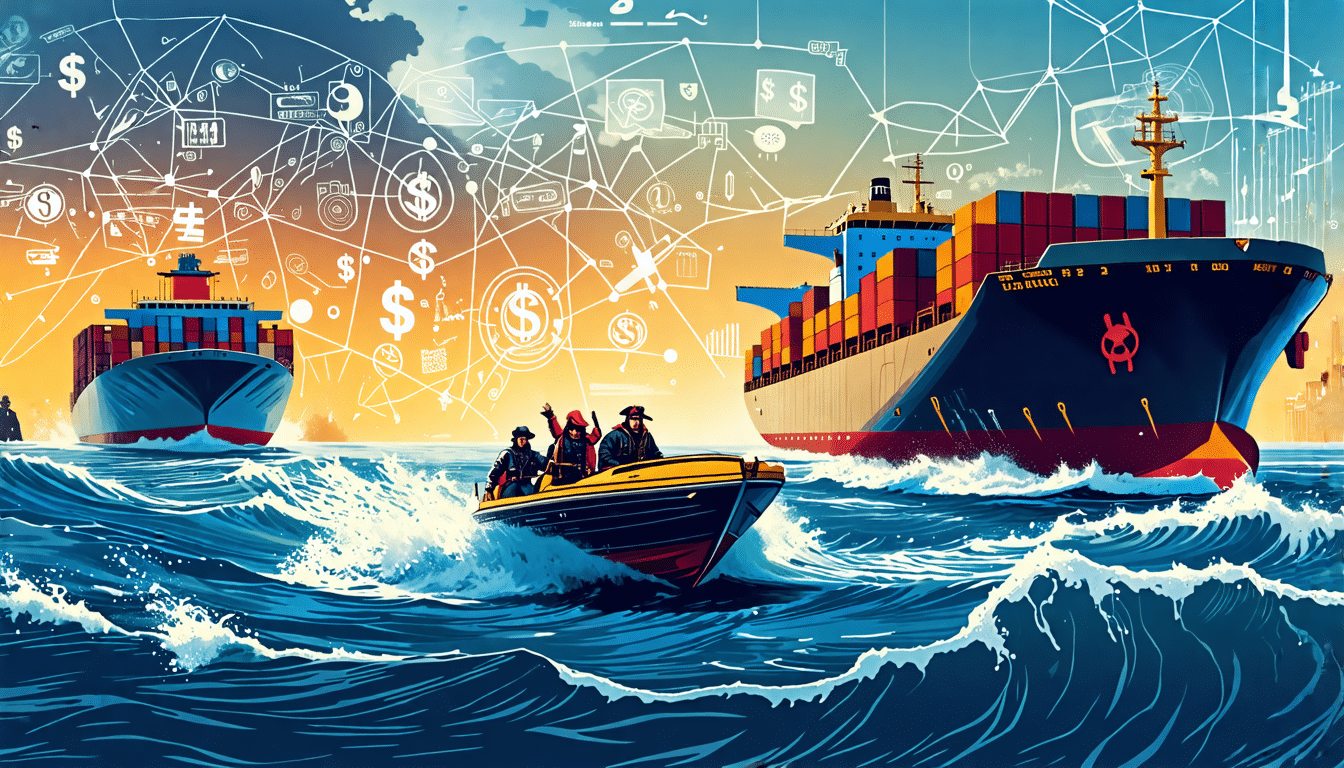
Modern-day pirates have become more sophisticated, employing advanced technology for navigation and coordination. They use fast boats, GPS, and satellite phones to track and intercept vessels. Additionally, poverty and political instability in many coastal regions motivate individuals to engage in piracy as a means of survival or profit.
To combat these modern piracy challenges, several countermeasures have been adopted. The primary approach involves international naval patrols in high-risk areas. Multinational task forces, such as NATO’s Operation Ocean Shield and the aforementioned Combined Maritime Forces, conduct regular patrols, escort merchant ships, and engage in direct action against pirate skiffs. These efforts have been instrumental in reducing successful pirate attacks, particularly in the Gulf of Aden.
Another effective measure is the implementation of Best Management Practices (BMP) for shipping. Developed by the shipping industry, BMPs provide guidelines for vessels to avoid, deter, and delay pirate attacks. Practices such as enhanced watchkeeping, the use of citadels (safe rooms), and the installation of physical barriers like barbed wire and water cannons have proven successful in mitigating risks.
Regional cooperation and capacity building are also essential components of modern piracy prevention strategies. Initiatives like the Djibouti Code of Conduct in the Western Indian Ocean and the Yaoundé Code of Conduct in the Gulf of Guinea aim to foster collaboration among coastal states. These agreements focus on improving maritime governance, sharing intelligence, and conducting joint exercises and training programs to bolster the capabilities of local navies and coastguards.
Furthermore, addressing the root causes of piracy requires long-term solutions that include political stability, economic development, and the establishment of effective governance structures. International aid and development programs aimed at creating alternative livelihoods can help reduce the economic incentives for piracy.
In conclusion, while piracy remains a significant threat to global maritime security, the combined efforts of international naval forces, regional cooperation, and industry best practices are making strides in combating the issue. Continuous adaptation to evolving tactics and addressing underlying socio-economic conditions are crucial for achieving sustained success in piracy prevention.
In conclusion, strategic maritime zones play a crucial role in global trade and security, influencing geopolitical relations significantly. These zones, identified based on their economic importance and susceptibility to security threats, are essential for understanding and mitigating maritime risks, especially piracy. Through a detailed examination of piracy-prone areas, such as the Gulf of Aden, the Strait of Malacca, and the West African coast, we observe historical patterns and current challenges that necessitate ongoing vigilance and robust countermeasures.
The historical overview of piracy hotspots highlights how certain maritime regions have been recurrent targets due to their strategic positions and high traffic volumes. Each case study reveals unique factors contributing to the prevalence of piracy, ranging from geopolitical instability and economic deprivation to inadequate maritime governance. Modern challenges further complicate these issues, with pirates adopting sophisticated tactics and exploiting technological advancements.
Preventive measures and international cooperation remain critical in addressing piracy. Successful strategies include enhanced naval patrols, improved maritime surveillance, and the strengthening of legal frameworks to prosecute offenders. Additionally, fostering regional collaboration and capacity-building among coastal states can significantly augment anti-piracy efforts.
Ultimately, the identification and analysis of piracy-prone areas underscore the need for continued investment in maritime security. Protecting these vital conduits of global commerce is indispensable for economic stability and international peace. Through concerted efforts, the global community can strive to ensure safer seas, promoting the free and secure movement of goods across the world’s oceans.